
Nmap6.45





Nmap, short for Network Mapper, is a widely used open-source tool designed for network discovery and security auditing. Developed by Gordon Lyon, Nmap is utilized by network administrators, security professionals, and hackers alike to scan networks and identify hosts and services. It is highly effective for network inventory, managing service upgrade schedules, and monitoring host or service uptime.
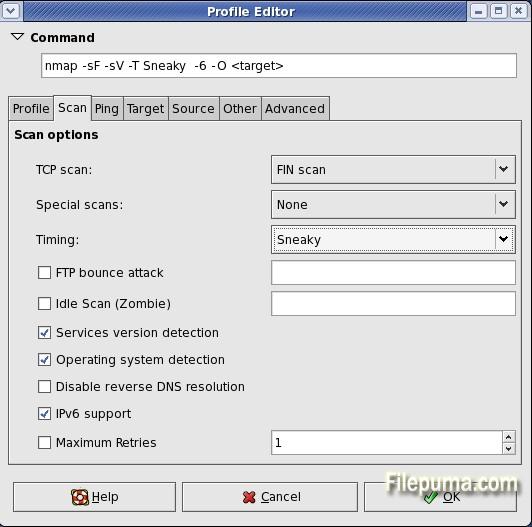
Nmap operates by sending specially crafted packets to targeted hosts and analyzing their responses. This process allows it to determine the status of various devices on a network, including which ports are open, which services are running, and which operating systems are in use. Nmap supports a wide range of scanning techniques, including TCP connect, SYN scan, UDP scan, and OS detection, allowing for thorough network analysis.
One of Nmap's key features is its scripting engine (NSE), which enables users to automate tasks such as detecting vulnerabilities, discovering malware, and performing advanced network reconnaissance. NSE scripts are written in Lua, a lightweight programming language, allowing users to extend Nmap’s functionality and customize scans according to their specific needs.
Nmap is supported on multiple platforms, including Windows, macOS, and Linux, making it accessible for users across different operating systems. Its robust features and ease of use make Nmap an essential tool for network security assessments and a fundamental component of many cybersecurity toolkits.
Key Features:
- Host Discovery: Finds live hosts on a network.
- Port Scanning: Scans open ports to see which services are running.
- Service Version Detection: Identifies software versions on open ports.
- OS Detection: Detects the operating system and device type of a host.
- Nmap Scripting Engine (NSE): Uses scripts for tasks like vulnerability detection and automation.
- Firewall Evasion: Bypasses firewalls and security systems during scans.
- Flexible Output: Supports multiple formats for results, like text, XML, and HTML.
- Stealth Scanning: Scans quietly to avoid detection by security systems.
- IPv6 Support: Works with both IPv4 and IPv6 networks.
- GUI (Zenmap): Offers a graphical interface for easier use.
What's New
- [NSE] Add ssl-heartbleed script to detect the Heartbleed bug in OpenSSL
- [NSE] Fixed an error-handling bug in socks-open-proxy that caused it to fail when scanning a SOCKS4-only proxy.
- [NSE] Improved ntp-info script to handle underscores in returned data.
- [NSE] Add quake1-info script for retrieving server and player information from Quake 1 game servers. Reports potential DoS amplification factor.
- [NSE] Add unicode library for decoding and encoding UTF-8, UTF-16, CP437 and other character sets to Unicode code points. Scripts that previously just added or skipped nulls in UTF-16 data can use this to support non-ASCII characters.
- When doing a ping scan (-sn), the --open option will prevent down hosts from being shown when -v is specified. This aligns with similar output for other scan types.
- [Ncat] Added support for socks5 and corresponding regression tests.
- [NSE] Add http-ntlm-info script for getting server information from Web servers that require NTLM authentication.
- Added TCP support to dns.lua.
- Added safe fd_set operations. This makes nmap fail gracefully instead of crashing when the number of file descriptors grows over FD_SETSIZE.
- [NSE] Added tls library for functions related to SSLv3 and TLS messages. Existing ssl-enum-ciphers, ssl-date, and tls-nextprotoneg scripts were updated to use this library.
- [NSE] Add sstp-discover script to discover Microsoft's Secure Socket Tunnelling Protocol
- [NSE] Added unittest library and NSE script for adding unit tests to NSE libraries. See unittest.lua for examples, and run `nmap --script=unittest --script-args=unittest.run -d` to run the tests.
- Updated bundled liblua from 5.2.2 to 5.2.3 (bugfix release)
- Added version detection signatures and probes for a bunch of Android remote mouse/keyboard servers, including AndroMouse, AirHID, Wifi-mouse, and RemoteMouse.
- [NSE] Added allseeingeye-info for gathering information from games using this query protocol. A version detection probe was also added.
- [NSE] Add freelancer-info to gather information about the Freelancer game server. Also added a related version detection probe and UDP protocol payload for detecting the service.
- [Ncat] Fixed compilation when --without-liblua is specified in configure (an #include needed an ifdef guard).
- [NSE] Add http-server-header script to grab the Server header as a last-ditch effort to get a software version. This can't be done as a softmatch because of the need to match non-HTTP services that obey some HTTP requests.
- [NSE] Add rfc868-time script to get the date and time from an RFC 868 Time server.
- [NSE] Add weblogic-t3-info script that detects the T3 RMI protocol used by Oracle/BEA Weblogic. Extracts the Weblogic version, as well
- Fixed a bug in libdnet with handling interfaces with AF_LINK addresses on FreeBSD >9 .Likely affected other *BSDs. Handled by skipping these non-network addresses.
- Fixed a bug with UDP checksum calculation. When the UDP checksum is zero (0x0000), it must be transmitted as 1's-complement -0 (0xffff) to avoid ambiguity with +0, which indicates no checksum was calculated. This affected UDP on IPv4 only.
- [NSE] Removed a fixed value (28428) which was being set for the Request ID in the snmpWalk library function; a value based on nmap.clock_ms will now be set instead.
- [NSE] Add http-iis-short-name-brute script that detects Microsoft IIS servers vulnerable to a file/folder name disclosure and a denial of service vulnerability. The script obtains the "shortnames" of the files and folders in the webroot folder.
- Idle scan now supports IPv6. IPv6 packets don't usually come with fragments identifiers like IPv4 packets do, so new techniques had to be developed to make idle scan possible.
- [NSE] Add http-dlink-backdoor script that detects DLink routers with firmware backdoor allowing admin access over HTTP interface.
- The ICMP ID of ICMP probes is now matched against the sent ICMP ID, to reduce the chance of false matches.
- [NSE] Made telnet-brute support multiple parallel guessing threads, reuse connections, and support password-only logins.
- [NSE] Made the table returned by ssh1.fetch_host_key contain a "key" element, like that of ssh2.fetch_host_key. This fixed a crash in the ssh-hostkey script. The "key" element of ssh2.fetch_host_key now is base64-encoded, to match the format used by the known_hosts file.
- [Nsock] Handle timers and timeouts via a priority queue (using a heap) for improved performance. Nsock now only iterates over events which are completed or expired instead of inspecting the entire event set at each iteration.
- [NSE] Update dns-cache-snoop script to use a new list of top 50 domains rather than a 2010 list.
- [NSE] Added the qconn-exec script , which tests the QNX QCONN service for remote command execution.
- [Zenmap] Fixed a crash that would happen when you entered a search term starting with a colon: "AttributeError: 'FilteredNetworkInventory' object has no attribute 'match_'".
- [Ncat] Added NCAT_PROTO, NCAT_REMOTE_ADDR, NCAT_REMOTE_PORT, NCAT_LOCAL_ADDR and NCAT_LOCAL_PORT environment variables being set in all --*-exec child processes.
Program available in other languages
User Reviews
User Rating
License:
Free
Requirements:
Windows All
Languages:
English
Size:
25.6MB
Publisher:
Updated:
Apr 14, 2014
Clean
Report Software
Latest Version
Old Versions
Developer's Software
Security Levels
To avoid any potential harm to your device and ensure the security of your data and privacy, our team checks every time a new installation file is uploaded to our servers or linked to a remote server and periodically reviews the file to confirm or update its status. Based on this checking, we set the following security levels for any downloadable files.
 Clean
Clean
It is highly likely that this software program is clean.
We scanned files and URLs associated with this software program in more than 60 of the world's leading antivirus services; no possible threats were found. And there is no third-party softwarebundled.
 Warning
Warning
This program is advertising supported and may offer to install third-party programs that are not required. These may include a toolbar, changing your homepage, default search engine, or installing other party programs. These could be false positives, and our users are advised to be careful when installing and using this software.
 Disabled
Disabled
This software is no longer available for download. It is highly likely that this software program is malicious or has security issues or other reasons.
Submit a Report
Thank you!
Your report has been sent.
We will review your request and take appropriate action.
Please note that you will not receive a notification about anyaction taken dueto this report.We apologize for anyinconvenience this may cause.
We appreciate your help in keeping our website clean and safe.

 Free Download
Free Download 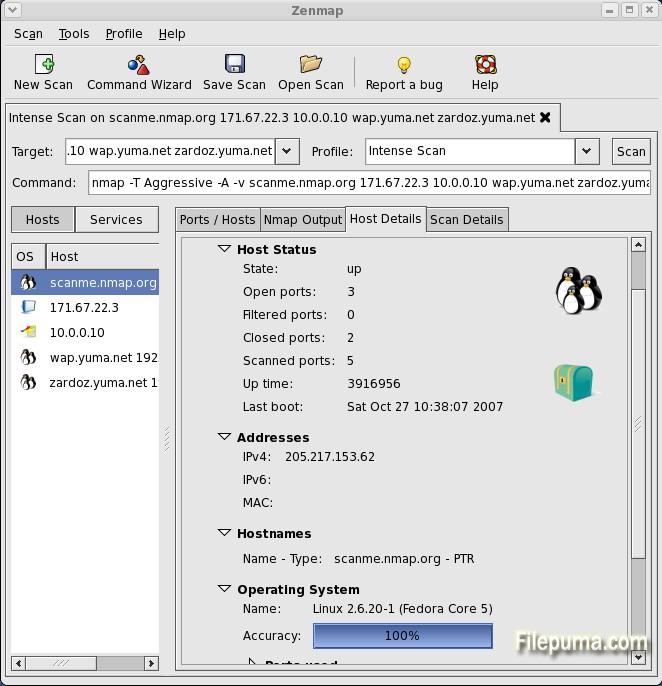


 Nmap 7.95
Nmap 7.95 Agnitum Outpost Security Suite 9.1
Agnitum Outpost Security Suite 9.1